National GSM networks vulnerability –
National security threat
UAB "Darseta" is a defense & law enforcement technology provider
for Government Intelligence and counterintelligence agencies.
GSMK OverSight
With the technical foundation of the SS7 protocol going back to the 70s, today's increasing network complexity requires strict policies and new tools to prevent fraud, hijacking or service disruption and espionage.
The original system definition for SS7 was never meant to offer authentication or access control. The protocol designers had a closed network in mind, with only trusted parties being connected. The same problem also exists with new LTE protocol "Diameter".
Those inherent system vulnerabilities have recently been publicly exposed, opening the door for systematic violation on a global scale.
The tremendous growth of independent entities with SS7 and "Diameter" access, including MVNOs and certain micro-operators, has made it easier for malicious actors to purposefully exploit the protocol's weaknesses.
Investigations commissioned by major network operators have shown a rapid increase in SS7-based and "Diameter-based" attacks.
The GSMK OverSight - GSM network security system for detecting atatcks on national GSM networks from foreign GSM networks via SS7 and "Diameter" signaling system.


Threats:
1. Subscriber privacy violations:
• track subscribers (worldwide, street level precision in cities, reading out geo coordinates directly)
• monitor when subscriber uses phone (SMS, call)
• retrieve authentication vectors for subscriber (enables decryption of over-the-air-traffic)
• find out phone numbers of subscriber
• show all caller IDs for incoming calls, even if they were suppressed by calling party
• compile detailed logs of all calls made or SMS sent or received by subscriber
• identify phone model in use by subscriber (via IMEI)
• read out call status
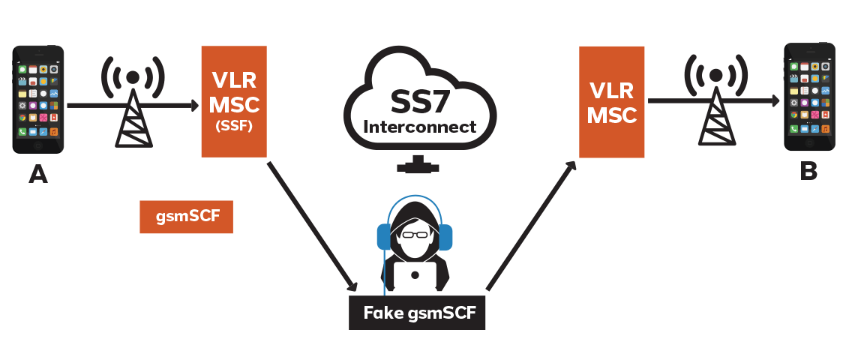
2. Illegal interception of calls, messages and data theft:
• intercept phone calls made or received by subscriber (man-in-the-middle)
• intercept SMS messages sent or received by subscriber (including two-factor authentication messages and mTANs sent by banks or online services)
• intercept and re-route Internet and other data connections
3. Denial of service (DoS):
• denial of service against operator network elements via specially crafted messages
• disable calls, SMS and data for subscriber
• denial of service against all subscriber’s using a network element
4. Billing fraud:
• transfer pre-paid balance to other subscribers
• make calls to premium rate numbers at the expense of subscriber
• make calls to premium rate numbers at the expense of operator
• setup data sessions at the expense and in the name of other subscribers
• disable billing of pre-paid subscribers (all calls and SMS free for subscriber)
• buy premium content in the name and at the expense of subscriber
• send SMS messages in the name and at the expense of subscriber
• remove pre-paid credit of subscriber with simulated calls
5. Manipulate network settings:
• simulate subscriber roaming in foreign network
• Subscriber profile modifications in HLR/HSS
• unauthorized use of APNs
• change outgoing caller ID to any number
• send official looking spam or phishing messages to subscriber
Solution:
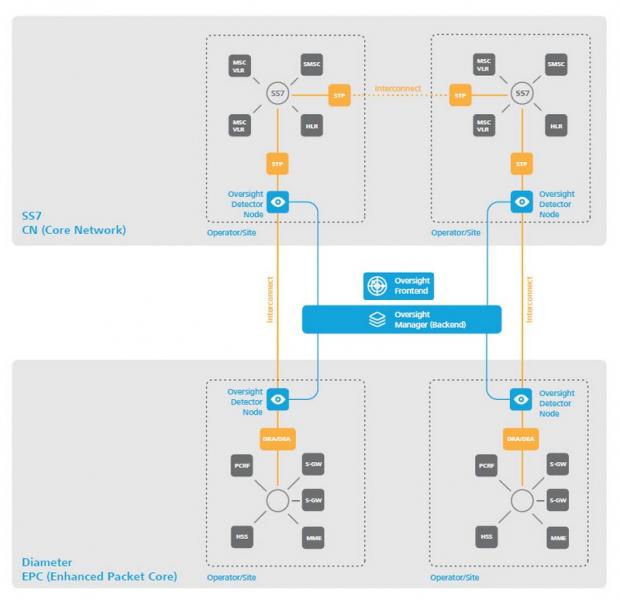
As a renowned industry leader in the field of strong encryption and network security, GSMK developed the Oversight system to enable comprehensive detection of network anomalies and reliable protection of SS7 and “Diameter” interconnections, finally transcending old-style STP filtering.
The Oversight system architecture provides seamless integration into existing signaling structures and complies with redundancy requirements within load balanced STP setups.
The Oversight network security system, building on a modular and scalable approach, consists of the Oversight Manager (deployed in National intelligence/counterintelligence agency and GSM Operator), which constitutes the centralized backend, as well as a number of a number of Oversight Detector or Oversight Protector nodes according to the number of interconnect STP nodes to be secured.
The Erlang/OTP-based software and runtime environment enable a highly parallel, fault-tolerant, real-time non-stop system with maximum availability and scalability for reliable SS7 and “Diameter” attack detection and parametrization.
Results:
1. Precise 24/7/365 counterintelligence information from which country via SS7 and “Diameter” are attacks executed.
2. Precise 24/7/365 counterintelligence information from which GSM operator via SS7 and “Diameter” are attacks executed.
3. Who are the “targets” in our country.
4. Gettining information about billing fraud and stpping them.

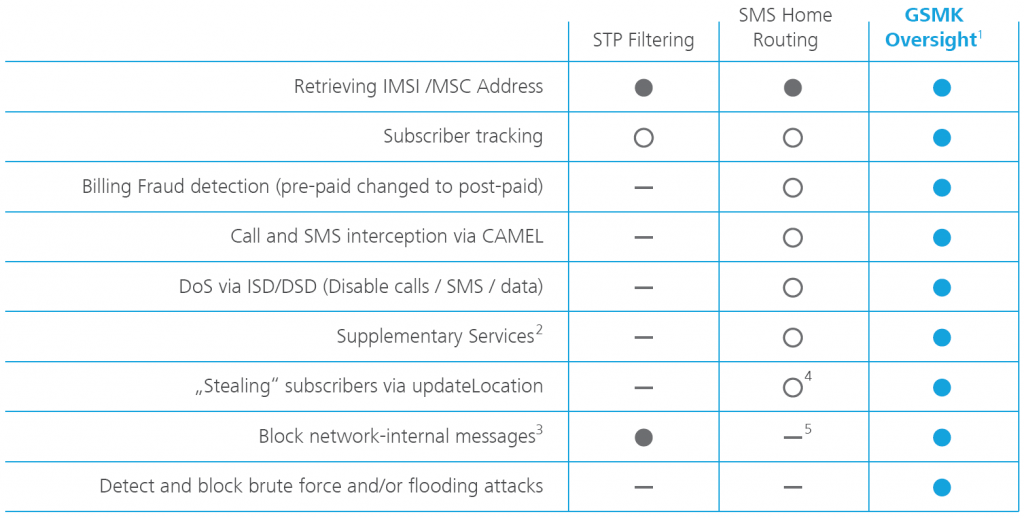
Standard tools and their effectiveness
compared with GSMK Oversight