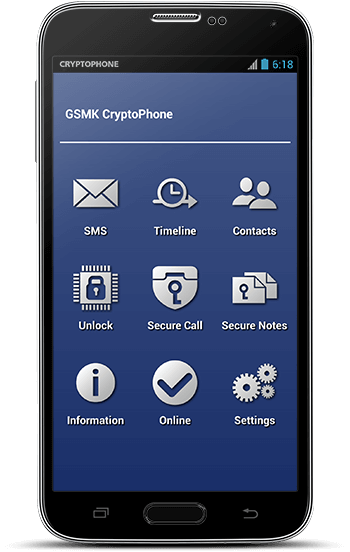
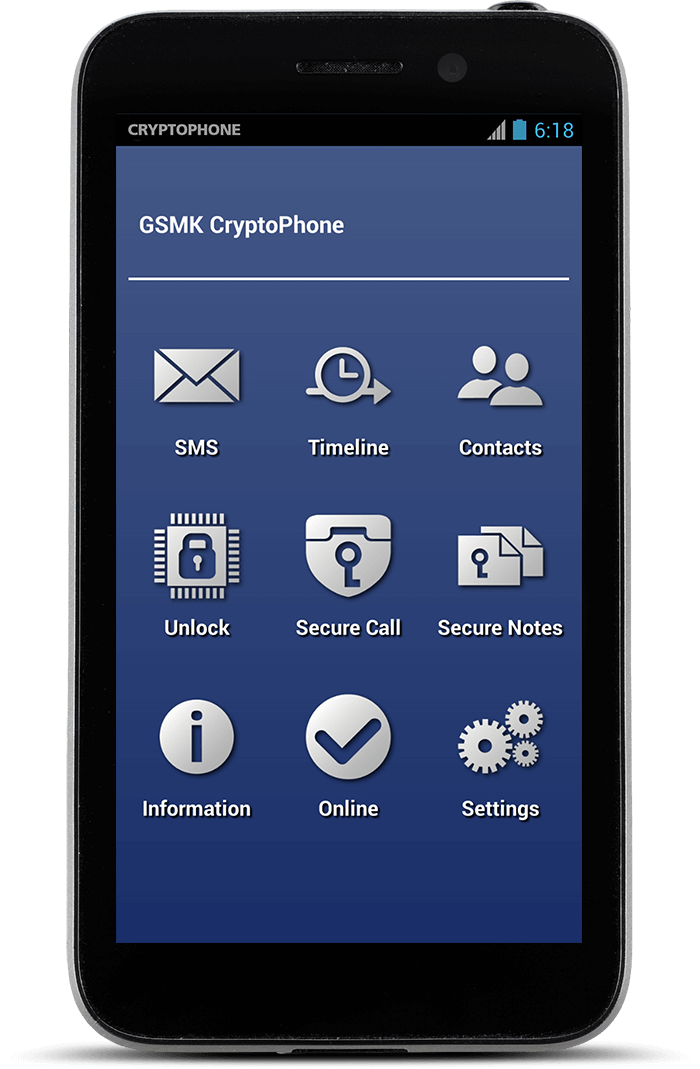
GSMK CryptoPhone secure mobile, landline and satellite products offer trustworthy 360-degree protection for encrypted communications across network borders:
Voice Encryption
GSMK CryptoPhones are the only secure telephones on the market that come with full source code published for independent security assessments. They feature the strongest and most secure encryption algorithms available today as well as the longest key lengths available on the global market, thereby offering true strategic security and peace of mind today and in the future. GSMK CryptoPhone secure mobile, fixed-line and satellite phones use latest-generation voice codecs and are fully compatible so that encrypted calls can be made across network borders – mobile to mobile, mobile to fixed-line, fixed-line to satellite, all with seamless interoperability.
Secure Messaging
All GSMK CryptoPhone secure mobile phones feature voice as well as SMS message encryption. With a 4096-bit Diffie-Hellman key exchange and 256-bit AES256 and Twofish symmetric encryption, they reliably protect confidential calls and messages without any compromises in usability. Secure international messaging comes standard with special features like self-destructing “Eyes Only” messages.
Mobile Device Security
A truly secure communication device must not only protect its communication links, it must also be able to withstand attacks against the device itself. To achieve this, all GSMK CryptoPhone secure mobile phones are based on a “hardened” operating system with granular security management and streamlined, security-optimized components and communication stacks. The hardened operating system reliably protects the device against outside attacks, thus offering true 360-degree protection when it counts most.
Phone protection:
- Hardened operating system: Secure Android OS built from source code with granular security management and streamlined, security-optimized components and communication stacks.
- Baseband firewall 2.0: Unique protection against over-the-air attacks with constant monitoring of base-band processor activity • Baseband attack detection and initiation of countermeasures • Detection of attempts to track the user’s location via SS7 or silent SMS.
- Configurable OS security profiles: Hardware module controller and permission enforcement module control access to network, data and sensors (camera, micro-phone, etc.), keeping you in control of your individual security policies.
- Encrypted storage system for contacts, messages and notes with smart folders protects date at rest against un-authorised access.